How Temporary Emails Reduce Phishing Risks
All You Need to Know About Phishing:
Cybercrime involves exploiting a system, people or a combination of both. Most phishing attacks on popular email and social media phishing websites rely on human weaknesses. Phishing involves creating false and deceptive websites to impersonate authentic entities. The goal of phishing is to defraud the victim of their private details to include user names, passwords, and/or financial details.
Phishing attacks can be broken down to different types based on a number of different classifications. The wide spread and most common phishing attacks on email systems are reported to originate from bogus emails that purport to be from reputable organizations and use the organizations logos and official template documents. These phishing emails either include links to fraudulent websites or attachments with malware incorporated that can either steal information or install malware to the system.
Smishing and Vishing involve the use of different communication systems, namely SMS and Voice, to obtain genuine information to use for illegitimate purposes.
Phishing attacks almost always have financial motives. Usually, cybercriminals try to access bank accounts and credit cards. In some cases, they attempt to hack corporate networks to access data and breach sensitive corporate data. Phishing attacks can result in heavy finances, and can harm individual and corporate reputations.
What are Temporary Emails
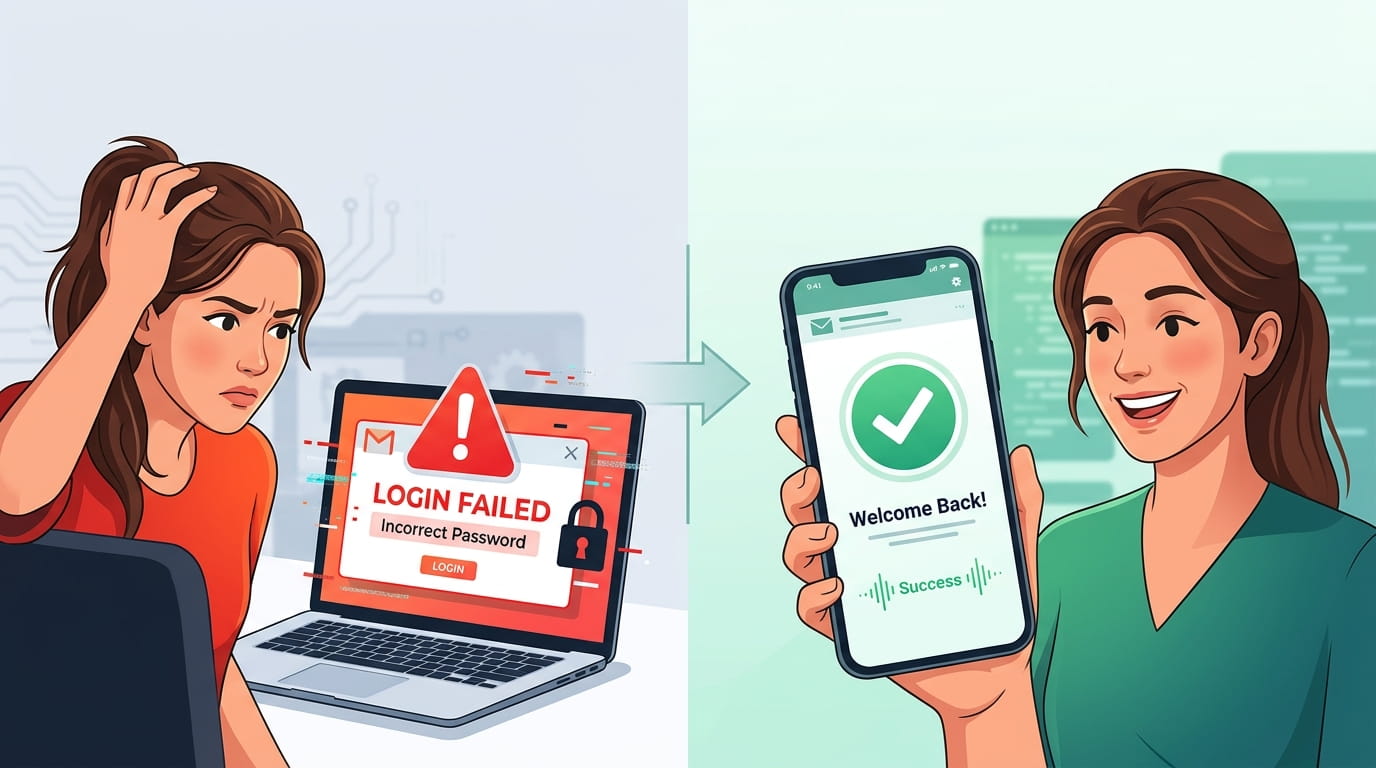
A temporary email is an email address, created for short-term use. It lets the user receive messages while avoiding exposure to real email accounts. Such addresses have an active time span of a few minutes and a few days. After that, the messages are deleted. The main advantage of temporary email usage is their emphasis on user protection and the enhancement of security. They even help with phishing attacks.
The protection importance of a temporary email cannot be emphasized enough. It acts as a buffer to the user from a malicious entity. Whenever the user is required to provide an email for a service, the user can provide a temporary email and change it subsequently.
When this is done, the user is less likely to be a phishing attack target, and the temporary email service provider is also less likely to be attacked directly.
There are a few reasons a ghost email can come in handy to shield your data from phishing attempts. For one, if you need to access sensitive information, you can create a ghost email to do this. This protects your real email from being used or sold. Ghost emails can come in handy when you’re signing up for things like free trials or one-time purchases. This protects your real email from being flooded with spam and protects your credited information from phishing attempts. This is useful when you need your information to be discrete, and the website you’re using doesn’t have a lot of guarantees and is poorly reviewed.
Temporary email accounts are very useful in this current digital age. Without compromising important personal information, they can improve your use of the internet and deal with phishing attempts with your information.
Temporary Emails Risks and Drawbacks
They can actually protect your information and improve your phishing attempts. Temporary emails allow you to shop online, sign up for free trials, and do things that you wouldn’t want with your information. If you have a temporary email that is dissolved after a few days, you are not risking as much and your personal information is not at stake. This also protects you from real phishing attempts.
Temporary email addresses also enable users to engage with websites without the risk of exposing themselves to incoming spam. Temporary email addresses provide users with anonymity, allowing them to take advantage of sites that potentially put them at risk. Malicious users won’t be able to send them spam or other harmful communications because their primary address remains confidential. During the process, users of temporary email addresses able to retain the overall safety and security of their primary emails.
Users of temporary email addresses also enjoy the benefit of closing down accounts without any hoops to jump through. If a site has users suspicious, they can simply close down their temporary address and eradicate the connection to their regulated identity while the left of the world can still access that site. An APWG study stated that more than 60% of phishing sites survive for fewer than 24 hours proves that the process of safeguarding access to information is efficient. Users of temporary email addresses can also safeguard themselves from the ultimate physical and emotional toll of phishing.
Overall, the use of Temporary Emails protects the personal information of users while decreasing the risks of phishing and spams. With temporary emails, users have the advantage of maintaining their privacy, decreasing spam, and being able to manage accounts easily, ensuring a safe and effective method for online security.
Best Temporary Emails
If you are registering on the Internet (for newsletters, social media accounts, online forums, websites, etc) en masse, it can reduce spam and phishing attempts to your preferred email to almost nothing by using temporary emails instead. However, the full potential of using temporary email services can only be realized when used in the exact manner temporary email services are intended to be used.
You want to use temporary email services, you are going to want to trust your email provider. Most trustworthy disposable email address services are from older companies. Good companies will not ask you to fill out personal information to register. Many good companies dont' want to know who you are and allow you to use their services without registering. Also, do your due diligence. Read other people's reviews.
You also want to manage your emails so that you are managing things more efficiently. Many services will let you rent your temporary email addresses longer to keep you from reaching out an an email. There are lots of sites that you can visit without registering to keep a inbox on.
For the best protection at all times, use temporary emails alongside security measures. For instance, use a VPN when you access emails to protect your data from people trying to access it. To add another layer of protection, use temporary emails to create a shield against attempts to break the system’s defenses and protect your primary emails. Furthermore, adding two-step authentication security ensures emails/pop-ups aren't bypassed by the system, making it a more effective temporary protection system during an online security frame.
At the end of the day, if you want to keep your primary email as safe as possible and use the most effective precautions against phishing attempts, email protection temporary systems should be used, and keep all the best recommended practices in mind.